In 2019, attackers stole over $1.6 million from the Ethereum Classic chain by spending the same tokens more than once - a textbook double spending attack that shook confidence in smaller blockchain networks. Double spending is the act of using the same digital asset in multiple transactions simultaneously, and it represents one of the most fundamental threats to the integrity of any digital currency system. This guide covers exactly how double spending works, the specific attack vectors criminals use, and how blockchain technology - along with your own transaction habits - keeps your assets safe.
⚡ Key Takeaways
- Double spending means using the same digital asset in more than one transaction before the first is confirmed
- The three primary attack types are: 51% attacks, Race attacks, and Finney attacks
- Consensus mechanisms (Proof of Work and Proof of Stake) are blockchain's core defense layer
- For Bitcoin transactions, waiting for 6 block confirmations is the standard security threshold
- Large, established networks like Bitcoin and Ethereum are practically immune - smaller PoW chains remain vulnerable
What Is Double Spending? The Core Problem Explained
Double spending is what happens when the same unit of digital currency is fraudulently used in two separate transactions. With physical cash, this is impossible - handing someone a $20 bill means you no longer have it. Digital money doesn't work that way. A digital file can be copied, and without a reliable system for tracking ownership, an attacker could theoretically broadcast the same funds to two different recipients and pocket the difference.
This is fundamentally different from how traditional finance handles the problem. Banks and payment processors maintain a central ledger - one authoritative record of who owns what. When you pay with a Visa card, Visa's centralized system instantly checks whether you have the funds and marks them as spent. The problem is solved by trusting a central authority. Decentralized cryptocurrency has no such authority, which is exactly what makes it trustless and censorship-resistant - but it also means the network itself must solve the double spending problem through consensus.
The academic framing of this challenge is the Byzantine Generals' Problem: how do geographically distributed parties reach agreement on a shared truth without a central coordinator? Satoshi Nakamoto's 2008 Bitcoin whitepaper was largely a solution to this problem, introducing a mechanism by which decentralized nodes could agree on transaction history without trusting any single participant.
How Double Spending Works - Step by Step
The mechanics are surprisingly straightforward once you understand the confirmation gap.
- Alice has 1 BTC. She decides to send it to Bob in exchange for goods.
- Alice broadcasts the transaction to the network. It enters the mempool - the waiting area of unconfirmed transactions - but has not yet been confirmed in a block.
- Before confirmation, Alice broadcasts a second transaction sending that same 1 BTC to Charlie (or back to herself). Both transactions are now competing in the mempool.
- Miners (or validators) pick up one of the transactions and include it in the next block. The one included first gets confirmed.
- The confirmed transaction wins. The other is invalidated by the network, because the UTXO (the specific unspent output Alice was spending) has already been consumed.
- Bob or Charlie receives the funds - but not both. The blockchain enforces that only one transaction can reference each UTXO.
The window of vulnerability is the time between when a transaction is broadcast and when it's confirmed. That gap - which can range from seconds to minutes depending on network congestion - is where every double spending attack is designed to strike.
Why Digital Assets Are Uniquely Vulnerable
Physical currency is self-authenticating. You can hold a banknote, verify its physical properties, and confirm it's in your possession. Once you hand it over, it's gone from your hand. Digital data has no such property - a file can be copied infinitely without degrading, and nothing about a digital transaction inherently prevents you from broadcasting the same data to multiple recipients.
Centralized systems solve this by appointing a trusted arbiter. PayPal knows your balance because PayPal maintains the ledger. The cost of this convenience is trust - you're relying on PayPal not to freeze your funds, censor your transactions, or go insolvent.
Decentralization removes that single point of control, which is where the Byzantine Generals' Problem becomes a real engineering challenge. Every node in the network must independently reach the same conclusion about transaction order, with no central authority to break ties. The mechanism for reaching that consensus - without trusting any single participant - is what separates robust blockchains from fragile ones.
The vulnerability gap between "transaction broadcast" and "transaction confirmed" is exactly where attackers strike. The question is how wide that gap is, and how expensive it is to exploit.

Types of Double Spending Attacks
There's no single method for double spending - attackers choose their technique based on the target network's vulnerabilities, their available resources, and whether they're attacking a merchant directly or reorganizing the chain itself. Five attack vectors are worth understanding in depth.
The 51% Attack - The Most Dangerous Variant
A 51% attack is the nuclear option of double spending - and it's the attack vector behind every major confirmed theft in blockchain history.
The mechanism: an entity that controls more than 50% of a network's total hash rate (in Proof of Work) can mine a private version of the blockchain in secret. They make a payment to a merchant - say, depositing cryptocurrency to an exchange - and while waiting for confirmation, continue mining their private chain. Once the exchange credits the deposit and the attacker withdraws the funds in another asset, they broadcast their longer private chain to the network. Because Bitcoin (and all PoW chains) recognizes the longest valid chain as canonical, the network accepts the attacker's version - which doesn't include the original deposit transaction. The attacker has effectively reversed a confirmed payment after already receiving the goods.
This is called a blockchain reorganization (reorg), and it's not always malicious - small reorgs happen naturally when two miners find valid blocks simultaneously. What makes a 51% attack different is its scale and intent.
Ethereum Classic (ETC) suffered multiple successful 51% attacks between 2019 and 2020. Attackers reorganized hundreds of blocks, successfully double-spending approximately $200,000 on Gate.io in one incident and attempting over $1.1 million on Coinbase. Bitcoin Gold (BTG) was hit in May 2018 - attackers executed a 51% attack and double-spent an estimated $18 million in a series of reorg transactions.
Why can't this happen to Bitcoin? The economics. Acquiring 51% of Bitcoin's hash rate would require hundreds of millions of dollars in ASIC hardware, plus ongoing electricity costs that dwarf any potential profit. The network's scale is its security. Small-cap PoW chains - especially newer ones with low mining participation - don't have that protection.
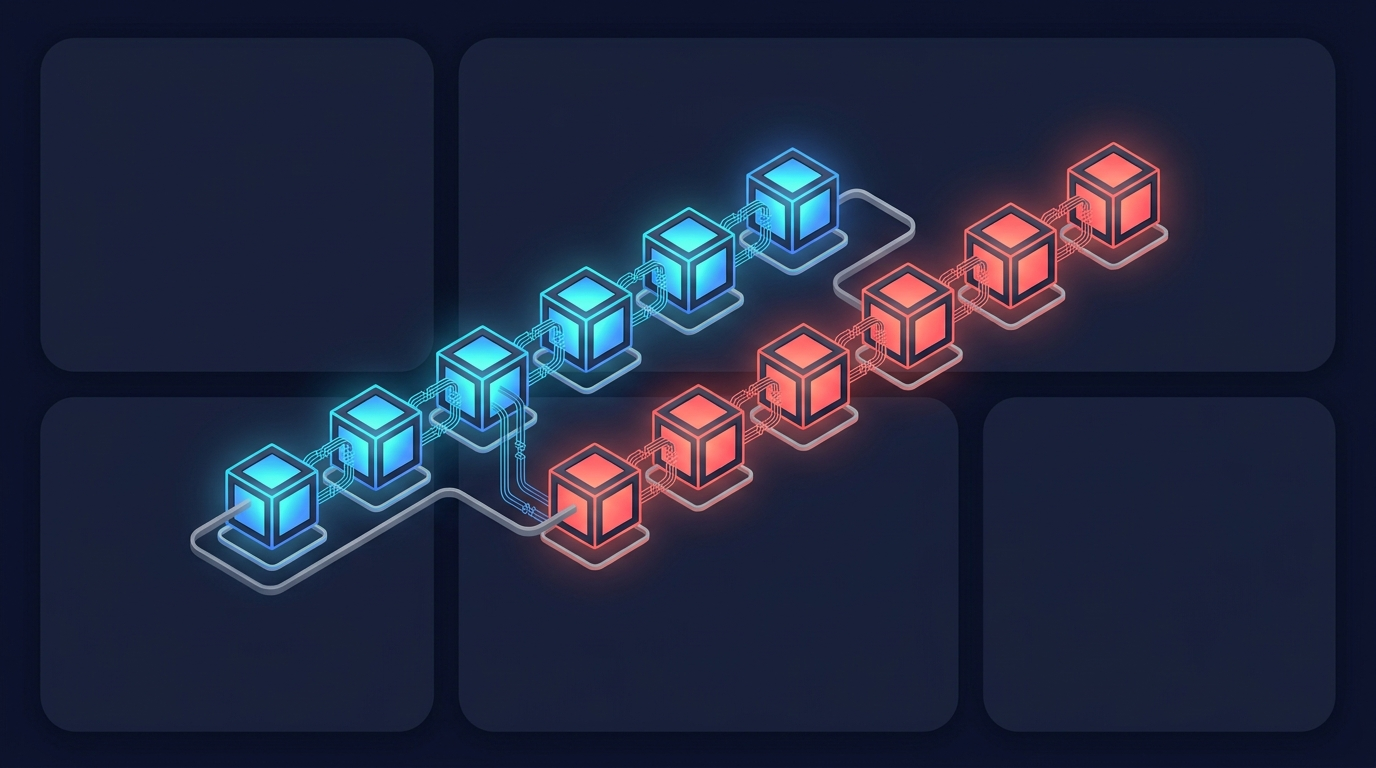
⚠ How a 51% Attack Enables Double Spending
NORMAL CHAIN
Block A → Block B → Block C (contains Alice→Bob payment) → Block D → Block E
ATTACKER'S PRIVATE CHAIN (longer - wins)
Block A → Block B → Block B' → Block C' → Block D' → Block E' → Block F'
When the attacker broadcasts their longer chain, the network switches. Block C and the Alice→Bob payment are reversed. Alice keeps her funds and the goods she received.
Race Attack and Finney Attack - Exploiting Confirmation Delays
Not every double spending attempt requires controlling a mining network. Race and Finney attacks target a simpler vulnerability: merchants who accept payments without waiting for block confirmations.
Race Attack: An attacker broadcasts two conflicting transactions at nearly the same time - one to a merchant, one back to themselves or a second wallet. Both enter the mempool simultaneously. If the merchant accepts the payment as "received" based on the unconfirmed broadcast (a zero-confirmation transaction), there's a chance the second transaction gets confirmed first, invalidating the merchant's payment. The attacker keeps both the goods and the funds.
Finney Attack: Named after cryptographer Hal Finney - one of Bitcoin's earliest contributors and the recipient of the first Bitcoin transaction - this attack requires the attacker to be a miner. The attacker pre-mines a block containing a transaction that sends funds back to themselves, but doesn't broadcast it. They then make a payment to a merchant using the same funds. Once the merchant accepts the zero-confirmation payment, the attacker broadcasts their pre-mined block, which - if it gets added to the chain - invalidates the merchant transaction.
Both attacks share the same practical countermeasure: never accept zero-confirmation transactions for significant amounts. Waiting for even 1-2 confirmations dramatically reduces the feasibility of both attacks. For amounts above a threshold you'd consider meaningful, 6 confirmations on Bitcoin is the accepted standard.
How Blockchain Prevents Double Spending
No single mechanism eliminates double spending entirely - blockchain uses a layered defense architecture where multiple independent systems would all need to be defeated simultaneously for an attack to succeed. On major networks, that's effectively impossible.
One nuance worth understanding: Bitcoin doesn't have absolute finality. A transaction is never technically "final" in a mathematical sense - a chain with more cumulative proof of work could theoretically always replace the current canonical chain. What it has is probabilistic finality: the cost of reversing a transaction with 6 confirmations (which would require re-mining 6 blocks plus all subsequent blocks faster than the rest of the network) is economically catastrophic. The probability approaches zero. This distinction matters for understanding why the "6 confirmations" recommendation exists.
Proof of Work vs Proof of Stake - How Each Prevents Double Spending
Both dominant consensus mechanisms attack the double spending problem from different economic angles. You can read a deeper breakdown in Zipmex's guide to Proof of Work vs Proof of Stake.
Proof of Work (PoW): Miners compete to solve computationally expensive cryptographic puzzles. The first to find a valid solution earns the right to add the next block and collect the block reward. This means rewriting blockchain history requires redoing all that computational work - and doing it faster than the entire honest network continues adding new blocks. Bitcoin's hash rate makes this catastrophically expensive: acquiring the necessary hardware and sustaining the electricity cost would run into hundreds of millions of dollars for even a brief attack window, with no guarantee of profit.
Proof of Stake (PoS): Instead of burning electricity, validators lock up cryptocurrency as collateral (their "stake"). Ethereum switched to PoS in September 2022. Validators are randomly selected to propose and attest to new blocks, weighted by their stake size. Malicious behavior - attempting to validate conflicting blocks, for instance - triggers slashing: automatic destruction of a portion of the validator's staked ETH. The attacker loses money directly from their own funds. Executing a successful double spending attack on Ethereum would require controlling 33%+ of staked ETH and accepting that a significant portion would be slashed.
A third variant, Delegated Proof of Stake (DPoS), used by chains like EOS, further distributes validation across elected delegates - providing faster transaction processing with a somewhat different security trade-off profile.
UTXO Model, Nonces, and Cryptographic Safeguards
Bitcoin's UTXO model deserves more credit than it typically gets in double spending discussions. Think of each UTXO like a physical banknote: when you spend it, it's destroyed and replaced by new "banknotes" of the correct denominations. If Alice has a 1 BTC UTXO and sends 0.6 BTC to Bob, the original UTXO is consumed and two new UTXOs are created - 0.6 BTC to Bob and 0.4 BTC back to Alice as change.
This structure means there's no such thing as a "balance" in Bitcoin at the protocol level - only a set of discrete, spendable outputs each with a unique identifier. The distributed ledger records which outputs have been spent; once spent, they can never be referenced again. Double spending a UTXO would require creating a transaction that references an already-consumed output - which every honest node will immediately reject.
Nonces add another safeguard. Each block contains a nonce - a cryptographic value that must meet specific hash conditions before the block is valid. Nonces are single-use by design; their values cannot be duplicated across blocks, which prevents replay attacks and ensures every block is uniquely cryptographically committed to its specific position in the chain.
SegWit (Segregated Witness), introduced to Bitcoin in 2017, improved transaction data integrity by separating signature data from transaction data. Among its benefits: it closes certain transaction malleability vulnerabilities that could theoretically be used to create apparent conflicts between transactions representing the same funds.
How to Protect Yourself from Double Spending as a User or Merchant
Double spending can affect you directly - especially if you accept crypto payments in any capacity. Understanding the practical defenses doesn't require deep technical knowledge.
✅ Double Spending Safety Checklist for Crypto Users & Merchants
- Wait for sufficient confirmations - 6 for Bitcoin, 12-20 for smaller chains; never accept zero-confirmation transactions for significant amounts
- Use established, high-security networks - Bitcoin and Ethereum have proven resilience; smaller PoW chains with low hash rates carry real risk
- Monitor network hash rate - sudden drops signal increased vulnerability to 51% attacks; tools like Crypto51 track this
- Consider Layer 2 for micro-payments - the Lightning Network processes Bitcoin payments off-chain with near-instant finality, suitable for small transactions where waiting 6 blocks is impractical
- Use exchanges with strong confirmation policies - reputable exchanges require multiple confirmations on crypto deposits; this is a feature, not friction
- Be cautious on small-cap chains - if you're transacting in a low-market-cap PoW cryptocurrency, apply higher confirmation thresholds before considering a transaction final
Even if you never mine a block or write a line of smart contract code, your transaction habits determine your exposure. The 6-confirmation standard for Bitcoin isn't arbitrary - it's calculated based on how much cumulative proof of work would need to be undone to reverse a transaction at that depth. By the time a Bitcoin transaction has 6 confirmations, reversing it would require an attacker to control more hash rate than the entire network and sustain it for over an hour. At that point, the attack is more expensive than the funds being targeted.
Double spending is a solved problem on major networks - but it remains a live risk on smaller chains.
Real-World Double Spending Attacks - Case Studies
Not all double spending attacks are theoretical. Here are confirmed cases that reveal the pattern clearly.
The pattern across every successful major attack is identical: low hash rate, proof of work, small-cap network. Ethereum Classic, Bitcoin Gold, and Litecoin Cash all share these characteristics. Ethereum Classic's hash rate at the time of the 2019 attacks was a fraction of Ethereum's - making majority control achievable with rental hash power from services like NiceHash, without purchasing a single ASIC.
Bitcoin's 2013 incident is instructive for a different reason. A software bug in the v0.8 client caused an unintentional chain split - two valid competing chains briefly coexisted. A merchant (OKPAY) confirmed a $10K deposit on one chain; miners coordinated to roll back 24 blocks on the longer chain, and the customer successfully double-spent on the restored canonical chain. This wasn't a premeditated attack - it was an accidental vulnerability that highlighted the importance of multiple confirmations even on the largest networks during edge-case events.
Bitcoin and Ethereum haven't experienced a successful adversarial double spending attack. The economic deterrent built into their scale makes the cost of attempting one exceed any plausible profit.

Future of Double Spending Prevention - Emerging Technologies
The arms race between attackers and protocol developers is ongoing, and the next generation of solutions goes well beyond incremental improvements to consensus mechanisms.
4 Technologies Shaping the Future of Double Spending Prevention:
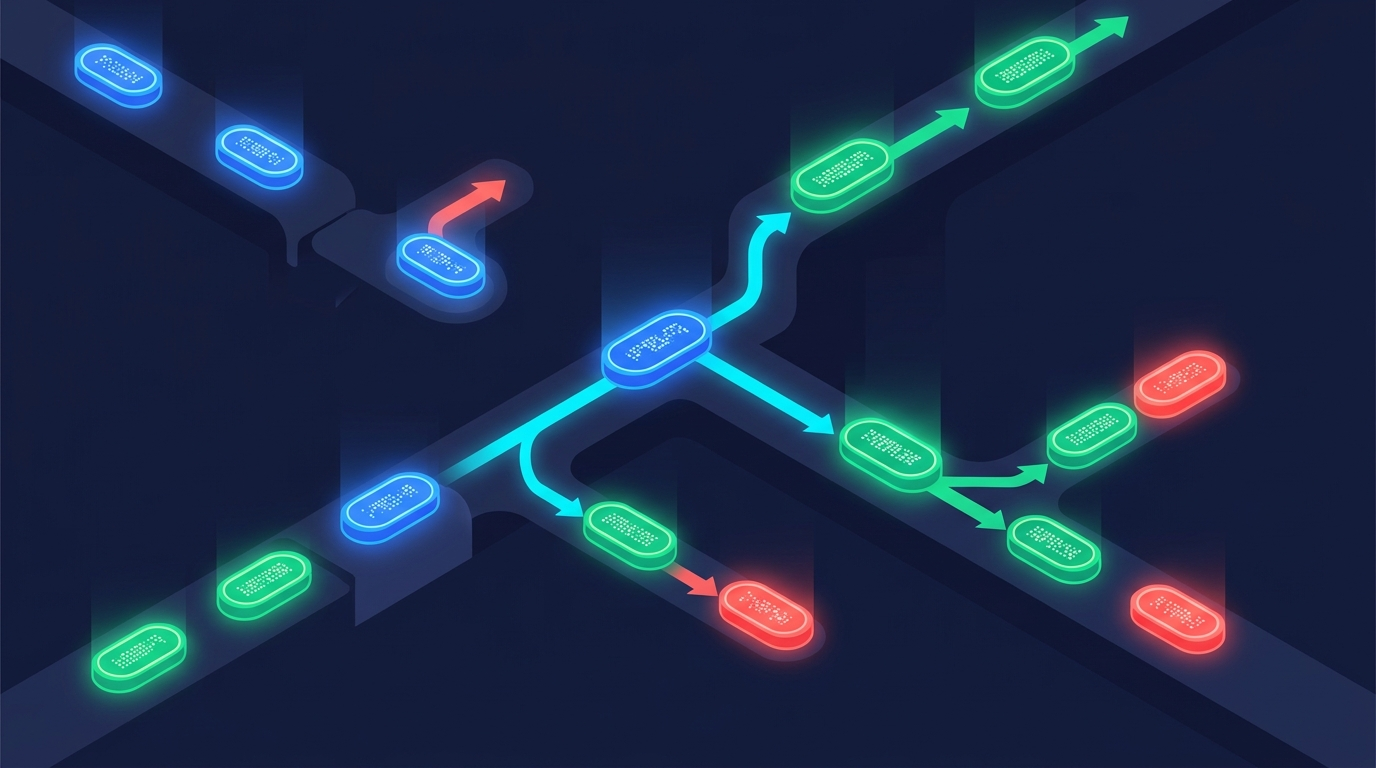
- Lightning Network - Bitcoin's primary Layer 2 solution processes transactions off-chain in private payment channels. Funds are locked in a multi-signature contract on-chain; transactions happen instantly within the channel and settle on-chain in a single final transaction. Double spending within a Lightning channel is structurally prevented by the channel's cryptographic state machine - attempting to broadcast an outdated channel state triggers automatic penalty clauses that transfer the attacker's funds to the counterparty.
- State Channels - A generalization of the Lightning concept applicable beyond simple payments. Multiple transactions happen off-chain between participants, with only the opening and closing states recorded on-chain. This reduces on-chain exposure to double spending during what would otherwise be a long confirmation window for many small transactions.
- Zero-Knowledge Proofs (zk-SNARKs) - Zero-knowledge proofs allow a transaction to be verified as valid without revealing the underlying data. In the context of double spending, zk-SNARKs enable a prover to demonstrate that a UTXO hasn't been previously spent without exposing wallet addresses or transaction history. Ethereum's rollup roadmap (zkSync, StarkNet) uses this technology to achieve faster finality on Layer 2 while inheriting Ethereum's Layer 1 security guarantees.
- Sharding - Dividing a blockchain into parallel processing lanes (shards) increases throughput but introduces new complexity around cross-shard transaction verification. Ethereum's long-term sharding roadmap includes mechanisms to prevent double spending across shards using cryptographic commitments that create atomic cross-shard transaction guarantees.
These technologies don't eliminate the double spending problem - they make it progressively more expensive and technically infeasible at each layer of the stack.
Conclusion - Double Spending in Context
Double spending isn't a theoretical curiosity - it's a real attack vector with a documented history of successful exploits, all concentrated in one specific category: small-cap, proof-of-work chains with low hash rates and insufficient decentralization.
The double spending problem on Bitcoin and Ethereum is essentially solved - not because the math rules it out absolutely, but because the economic cost of an attack exceeds any realistic profit by orders of magnitude. On-chain verifiability is the foundation that makes this true: every transaction is publicly auditable, every block is cryptographically committed to its history, and every consensus rule is enforced by thousands of independent nodes with no central coordinator that can be bribed or coerced.
The risk lives at the edges of the ecosystem. New chains, low-liquidity networks, and PoW projects launched without sufficient mining participation carry real exposure. The confirmation thresholds and security practices covered in this guide apply most critically in those environments.
Platforms that prioritize trustless, verifiable architecture - where users control their own funds and every outcome is auditable on-chain - reflect exactly where the industry's security trajectory leads. Transparency isn't a feature you add later; it's the mechanism that makes double spending economically irrational in the first place.
Crypto trading and digital asset transactions involve substantial risk of loss. Nothing in this article constitutes financial or investment advice. Always conduct your own research and assess your risk tolerance before transacting in cryptocurrency.
Last updated: April 2026.
Frequently Asked Questions
What is double spending in simple terms?
Double spending means using the same digital currency to pay two different people at the same time - spending money you've already spent. With physical cash, this is impossible because handing over a banknote removes it from your possession. Digital money is different: it's a data file that can theoretically be copied and broadcast to multiple recipients before any transaction is confirmed. Blockchain prevents double spending by maintaining a public record of every transaction, ensuring each unit of currency can only be referenced once in a valid transaction chain.
Why is double spending a problem for cryptocurrency?
Cryptocurrency's core value proposition is that it functions as money without a central bank or payment processor. But removing the central authority means the network itself must prevent fraud. Without a reliable anti-double-spending mechanism, anyone could receive payment and immediately broadcast a second transaction spending the same funds elsewhere. This would destroy trust in the currency - no merchant would accept payment they can't rely on being valid. Solving the double spending problem is literally the reason blockchains exist as a data structure.
How does Bitcoin prevent double spending?
Bitcoin prevents double spending through three interlocking mechanisms. First, every transaction is broadcast to thousands of nodes that independently verify it doesn't conflict with previously confirmed transactions. Second, the UTXO model ensures each spendable output can only be consumed once - once spent, it's permanently marked and any transaction referencing it again is rejected. Third, Proof of Work consensus makes rewriting confirmed transaction history prohibitively expensive: reversing a transaction with 6 confirmations would require controlling more hash rate than the entire network for over an hour.
What is a 51% attack and how does it relate to double spending?
A 51% attack occurs when a single entity controls more than half of a blockchain network's total mining power (hash rate). With majority control, the attacker can mine a private chain faster than the public network, execute a payment, receive goods or withdraw funds, then broadcast their longer private chain - which doesn't include the original payment. The network switches to the longer chain and the payment is reversed. The attacker keeps both the funds and whatever they received. Ethereum Classic and Bitcoin Gold have suffered confirmed attacks of this type.
What is a Race Attack in blockchain?
A Race Attack targets merchants who accept unconfirmed cryptocurrency transactions. The attacker broadcasts two conflicting transactions simultaneously - one to the merchant's wallet and one back to themselves - hoping the self-payment gets confirmed first while the merchant treats the unconfirmed broadcast as received payment. The attack only works against merchants accepting zero-confirmation transactions. The defense is straightforward: wait for at least 1-2 confirmations before considering any payment received, and require 6 for high-value transactions.
How many confirmations do you need to avoid double spending on Bitcoin?
Six confirmations is the widely accepted standard for Bitcoin transactions of significant value. Each confirmation means one additional block has been mined on top of the block containing your transaction. Reversing a 6-confirmation transaction would require an attacker to re-mine those 6 blocks plus all subsequent blocks faster than the entire honest network - a task that would cost hundreds of millions of dollars. For smaller amounts, 1-3 confirmations is considered sufficient. Major exchanges typically require 3-6 Bitcoin confirmations before crediting deposits specifically to guard against double spending attempts.
Which blockchains are most vulnerable to double spending attacks?
Small-cap, Proof of Work blockchains with low hash rates are the highest-risk category. When a chain's total mining power is small enough that majority control can be rented cheaply via hash-rental markets, a 51% attack becomes economically viable. Chains launched as Bitcoin forks - maintaining PoW without Bitcoin's mining ecosystem - are particularly exposed in their early stages. Key metrics to check: hash rate relative to the leading PoW chain using the same algorithm, mining power concentration, and whether the chain has survived previous attack attempts.

